Cybersecurity Insights & Expert Guidance
Stay ahead of evolving threats with actionable cybersecurity insights, real-world case studies, and expert guidance from Inventive HQ's security team.
Featured Series

Healthcare Cybersecurity
Healthcare Cybersecurity
HIPAA Compliance Services for Healthcare | Avoid $1.5M Fines
We help healthcare organizations and their business associates achieve and maintain HIPAA compliance without the complexity, confusion, or six-figure consultant fees. Plans starting at $2,995/month.

Virtualization History: 1960s Mainframes to Cloud
Discover how virtualization technology evolved from IBM mainframes in the 1960s to today’s enterprise cloud solutions, revolutionizing IT infrastructure and business operations.
HIPAA Security Assessment & Gap Analysis Workflow
Systematic workflow for conducting comprehensive HIPAA Security Rule assessments, identifying compliance gaps, and preparing for OCR audits in 2025.

How InventiveHQ Delivers Up to 59% GCP Savings for SMBs
SMBs cut their GCP spend by up to 59% with the right approach. That’s not a marketing promise—it’s the documented result achieved by InventiveHQ clients.
Business Continuity Solutions | Ransomware Defense
What if ransomware hit your business tomorrow morning? With InventiveHQ’s proven approach, recovery isn’t just possible—it’s guaranteed.
Compliance Services | SMB Solutions
What if compliance stopped being a burden and became a competitive advantage? Discover InventiveHQ’s systematic methodology that transforms regulatory complexity into manageable business processes tha...

PowerShell Get Printers: Bulk Add TCP/IP Network Printers
Transform tedious manual printer installation into efficient automated workflows for enterprise environments

How to Autoscale Your WordPress Site on AWS
WordPress powers over 27% of websites globally, making it the world’s most popular content management system. While managed WordPress hosting offers simplicity, businesses often need more control, cus...
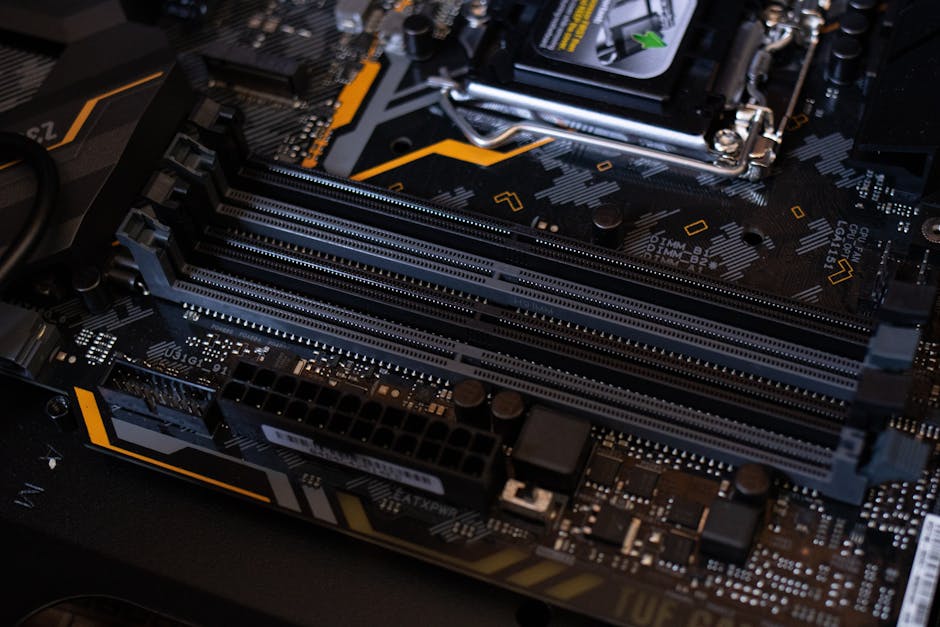
Best Motherboard & CPU for Virtualization | Hardware Selection Guide 2025
Master hardware selection for optimal virtualization performance and scalability

How to Create CLI Utilities with Python
Build cross-platform command-line tools using argparse, Click, and Typer for streamlined workflows

How to Enable BranchCache on NetApp CIFS Shares
In distributed environments, remote offices often struggle with slow file access due to high latency and limited WAN bandwidth.BranchCache, a WAN optimization feature from Microsoft, solves this by al...

How to Install cURL on Windows: 5 Easy Methods (2025 Guide)
Install cURL on Windows using PowerShell, Chocolatey, or manual download. Complete guide with step-by-step instructions for all methods.

Java Send Email Programmatically | SMTP Guide
Complete guide with setup instructions and code examples for SMTP integration
Git Squash Commits | Streamline History Guide
Master Git rebase to create cleaner, more professional commit histories
Page 11 of 64 • 959 articles total
Stay Ahead of Cyber Threats
Get expert cybersecurity insights, threat intelligence, and best practices to protect your business.