Cybersecurity Insights & Expert Guidance
Stay ahead of evolving threats with actionable cybersecurity insights, real-world case studies, and expert guidance from Inventive HQ's security team.
Featured Series

Python Objects and Classes Guide | OOP Fundamentals
Master object-oriented programming in Python with practical examples and best practices for efficient development

Python Pytest Testing | Unit Test Guide
Master Python unit testing with pytest framework to automate testing, improve code quality, and catch bugs early in development.

Python String Operations | Text Processing Guide
Master essential Python string operations including concatenation, manipulation, searching, and tokenization with practical examples.

Python Switch Statement: Match-Case & Alternatives Guide
Discover Python alternatives to switch statements using if-elif chains and dictionary lookups for cleaner, more efficient code.

Python Virtual Environments: Complete Setup and Management Guide (venv)
Create and manage Python virtual environments with venv. Prevent dependency conflicts and improve your Python development workflow.
Risk Assessment Frameworks | NIST & ISO
The Critical Decision Every SMB Leader Must Make

Cloud Cost Management for SMBs | Eliminate Waste & Save

Scaling SMB IT: From Reactive Fixes to Strategic Growth
Every growing business hits a point where its IT setup starts to show cracks. What worked when you had ten employees, a few SaaS subscriptions, and a “call the IT guy when something breaks” approach n...

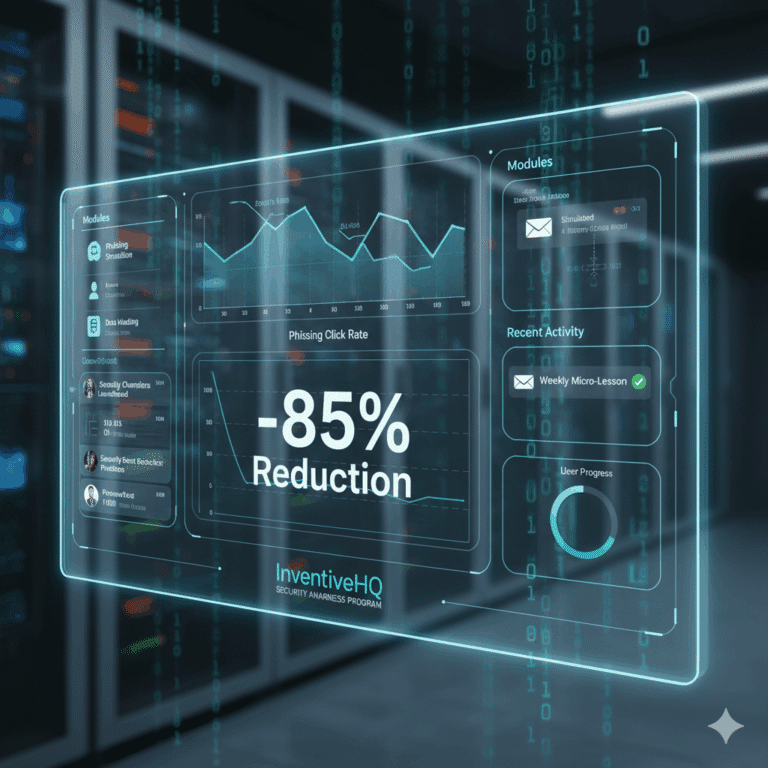
Security Awareness Training: Build a Human Firewall
From $499/month for fully managed training programs using Microsoft or KnowBe4. We help growing businesses transform employees into your strongest defense, reduce phishing clicks by 85%, and build a s...

Security Operations Center (SOC)
Get 24/7 Security Operations Center (SOC) monitoring that catches threats before they become business-ending disasters.

Secure Password & Authentication Flow Workflow
Master the complete secure password and authentication workflow used by security teams worldwide. This comprehensive guide covers NIST 800-63B password guidelines, Argon2id hashing, multi-factor authentication, session management, brute force protection, and account recovery with practical implementation examples.
Security Policies Nobody Reads | SMB Guide
The Shocking Truth About Security Policy Effectiveness
Security Policies
We create custom security policies that employees actually follow — protecting your data, meeting compliance requirements, and building a culture of security that scales with your business.

Server Virtualization Guide | Complete Introduction
Discover how server virtualization enhances efficiency, reduces costs, and scales with VMware, Hyper-V, and open-source platforms.

SOC 2 Compliance Services - Get Certified in 3-6 Months
We help B2B SaaS and technology companies achieve SOC 2 Type I and Type II certification in months, not years — turning compliance from a sales blocker into your competitive advantage.
Page 13 of 62 • 920 articles total
Stay Ahead of Cyber Threats
Get expert cybersecurity insights, threat intelligence, and best practices to protect your business.